Windows 10 Crypto API Spoofing
Microsoft has released a new security patch for a vulnerability that could affect millions of Windows 10 Users world wide.
A decades old API
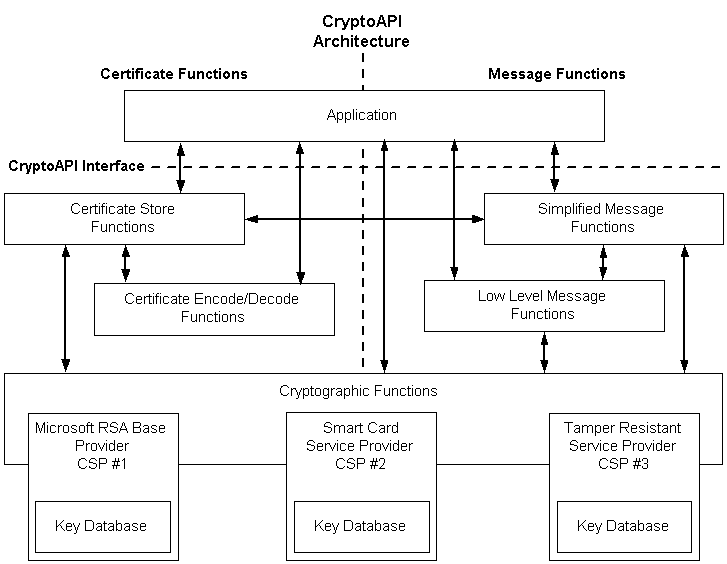
The decades old CryptoAPI tool validates and signs packages/software which could be utilized by hackers/developers to sign and execute illegitimate software thus would allow users to run anything without user’s nor Antivirus/Internet Security software’s notice.
Microsoft mentioned that the vulnerability could also allow hackers to change or modify encrypted communications.
It’s important to mention that CryptoAPI is a legacy API that’s being replaced by a new CNG (Cryptography Next Generation API) which also supports CryptoAPI.
CryptoAPI Key Storage Architecture
Download Patch
Direct Download
https://www.catalog.update.microsoft.com/Search.aspx?q=KB4528760
CVE
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0601
Windows 2008 R2, Windows 7 RDP
A day ago Microsoft released two very important security patches on May 14, 2019.
One of these patches has been detected in the RDP service (CVE-2019-0708) which affects Windows 7 and Windows 2008 R2.
According to MS’s Article a remote code execution vulnerability exists in Remote Desktop Services – formerly known as Terminal Services – when an unauthenticated attacker connects to the target system using RDP and sends specially crafted requests.
No Authentication or Interaction needed
This vulnerability is pre-authentication and requires no user interaction. An attacker who successfully exploited this vulnerability could execute arbitrary code on the target system.
An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
When look at CVE-2019-0708, which is related to the RDP service, we see that attackers are able to run code on systems by sending specially produced packages without any user interaction and authentication and manage to install malware like Ransomware or other execution files.
Download Patch
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708
Windows 2008R2, 2012R2, 2016 and 2019 DHCP
The other one is in the DHCP service (CVE-2019-0725), and both vulnerabilities are very critical.
A memory corruption vulnerability exists in the Windows Server DHCP service when processing specially crafted packets. An attacker who successfully exploited the vulnerability could run arbitrary code on the DHCP server.
Download Patch
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0725
Sources:
Microsoft, NSA, Other Security Researchers