The Story
After the disastrous exploit that was found in Microsoft Exchange Servers lots of corporations started immediately patching their servers with the latest Cumulative update and Security patches. The question is would those patches be enough if the server is already hacked or have a backdoor installed already?
What are those 0-day exploits ?
The vulnerabilities recently being exploited were CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 which are part of alleged “State-sponsored Chinese group” according to Microsoft.
Let’s get into details of those exploits one by one:
CVE-2021-26855 is a server-side request forgery (SSRF) vulnerability in Exchange which allowed the attacker to send arbitrary HTTP requests and authenticate as the Exchange server.
CVE-2021-26857 is an insecure deserialization vulnerability in the Unified Messaging service. Insecure deserialization is where untrusted user-controllable data is deserialized by a program. Exploiting this vulnerability gave HAFNIUM the ability to run code as SYSTEM on the Exchange server. This requires administrator permission or another vulnerability to exploit.
CVE-2021-26858 is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
CVE-2021-27065 is a post-authentication arbitrary file write vulnerability in Exchange. If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. They could authenticate by exploiting the CVE-2021-26855 SSRF vulnerability or by compromising a legitimate admin’s credentials.
How to proceed ?
Microsoft released couple of tools that could diagnose your servers and check if you already have been infected with a backdoor or any of these nasty malware and also remove those infected files or clean them and ask you for a restart if it’s required.
Tools:
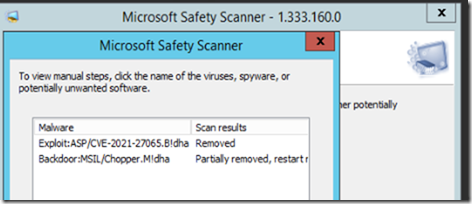
- MSERT (Microsoft Safety Scanner) detects web shells, Download here .
- Health Checker (Scans your server for any vulnerabilities and whether you have updated Server CU and installed patches). Download here
- Exchange WebShell Detection (A simple PowerShell that is fast and checks if your IIS or Exchange directory has been exploited). Download here
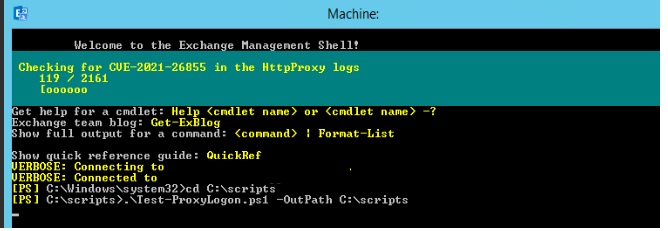
- Scan your exchange server for proxy logon:
https://github.com/microsoft/CSS-Exchange/tree/main/Security - Microsoft very recently created a mitigation tool for Exchange on-premises that would rewrite url for the infected servers and recover the files that were changed. You can download the tools from this github link.
https://github.com/microsoft/CSS-Exchange/tree/main/Security
Copy the Test-ProxyLogon code into Notepad
Save As “Test-ProxyLogon.ps1” with the quotes in your C:\Temp folder
Run in Exchange Management Shell: .\Test-ProxyLogon.ps1 -OutPath C:\Temp
Scan Result
Scan result should show you the following if your servers has been exploited already.
This will remove the infections and asks for a restart.
References:
https://www.microsoft.com/security/blog/2021/03/02/hafnium-targeting-exchange-servers/